Diffie-Hellman Key Exchange | Microschool Dev
Diffie-Hellman (DH) key exchange is a cryptographic protocol enabling two parties to establish a shared secret key over an insecure communication channel…
Contents
Overview
The genesis of Diffie-Hellman key exchange traces back to the mid-1970s, a period ripe with innovation in cryptography. The concept of public-key cryptography was independently conceived by [[Ralph Merkle|Ralph Merkle]], reportedly in his 1974 Stanford PhD dissertation. It was [[Whitfield Diffie|Whitfield Diffie]] and [[Martin Hellman|Martin Hellman]] at [[Stanford University|Stanford University]] who first published a practical method for key exchange in their seminal 1976 paper, "New Directions in Cryptography." This paper, a landmark in the field, also introduced the concept of public-key cryptography itself. The work built upon earlier, classified research conducted at [[GCHQ|Government Communications Headquarters]] in the UK, where [[Malcolm Williamson|Malcolm Williamson]] had developed a similar protocol, though it remained secret for some time. The publication by Diffie and Hellman, however, democratized the idea, sparking widespread research and development in secure communications.
⚙️ How It Works
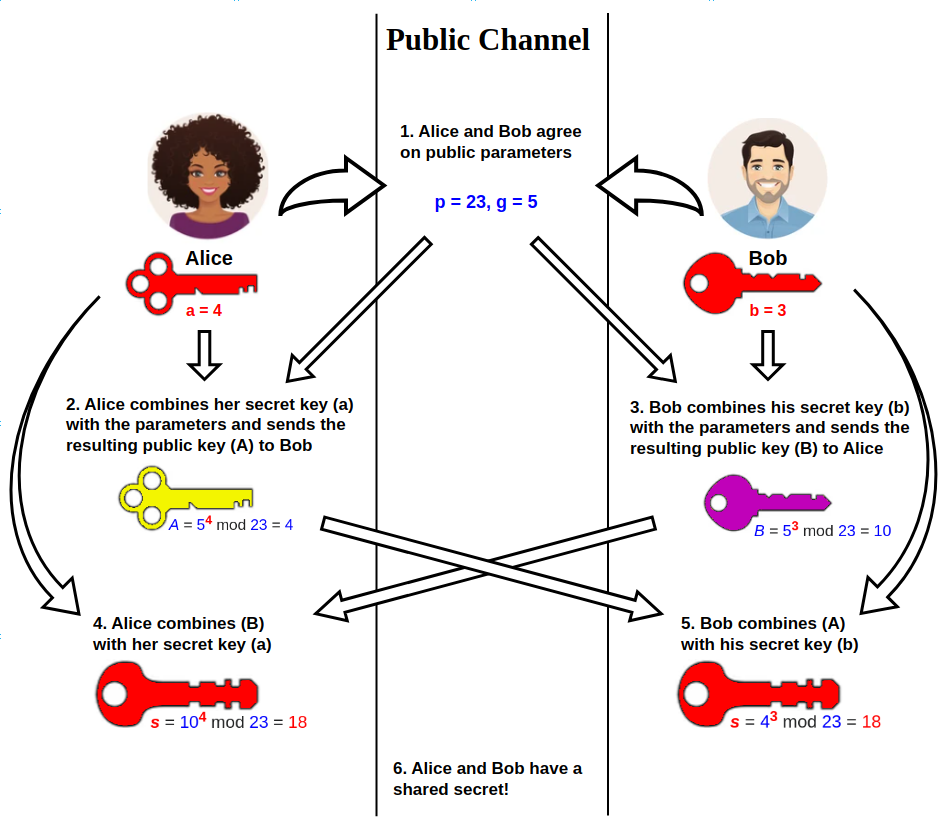
At its heart, Diffie-Hellman relies on modular arithmetic and the difficulty of the discrete logarithm problem. Two parties, Alice and Bob, agree on a large prime number 'p' and a generator 'g' (both public). Alice chooses a secret random integer 'a' and computes A = g^a mod p, sending A to Bob. Bob, independently, chooses a secret random integer 'b' and computes B = g^b mod p, sending B to Alice. Crucially, Alice can then compute the shared secret by raising Bob's public value B to her secret exponent 'a': S = B^a mod p = (g^b)^a mod p. Similarly, Bob computes S = A^b mod p = (g^a)^b mod p. Both arrive at the same secret 'S' without ever transmitting their private exponents 'a' or 'b'. An eavesdropper, knowing only 'p', 'g', 'A', and 'B', faces the computationally infeasible task of deriving 'a' or 'b' from these public values.
📊 Key Facts & Numbers
The security of Diffie-Hellman is directly tied to the size of the prime modulus 'p'. For robust security against modern computational power, key lengths are important, with larger primes offering greater security. The computational cost of generating these large primes and performing the exponentiation operations scales significantly with bit length. For instance, a 2048-bit DH key exchange might take milliseconds on a typical server. The number of possible shared secrets is related to the prime 'p', meaning a 2048-bit prime offers a very large number of potential keys. As of 2024, the [[Internet Assigned Numbers Authority|IANA]] recommends specific groups (pre-defined 'p' and 'g' values) for DH, with RFC 8731 specifying groups up to 8192 bits for enhanced security.
👥 Key People & Organizations
The protocol is intrinsically linked to its inventors, [[Whitfield Diffie|Whitfield Diffie]] and [[Martin Hellman|Martin Hellman]], both researchers at [[Stanford University|Stanford University]] who co-authored the foundational 1976 paper. [[Ralph Merkle|Ralph Merkle]] independently conceived of public-key cryptography and key exchange methods around the same time, publishing his work later. [[Malcolm Williamson|Malcolm Williamson]] of [[GCHQ|Government Communications Headquarters]] developed a similar protocol earlier but it remained classified. In the realm of implementation and standardization, organizations like the [[Internet Engineering Task Force|IETF]] play a crucial role through their RFCs (Request for Comments), such as RFC 7919 which specifies the use of DH groups in the [[Transport Layer Security|TLS]] protocol. Companies like [[Cloudflare|Cloudflare]] and [[Akamai Technologies|Akamai]] are major deployers of DH-based security for web traffic.
🌍 Cultural Impact & Influence
Diffie-Hellman exchange fundamentally altered the landscape of secure digital communication, moving it from a domain of specialized government agencies to one accessible to everyday users. It enabled the widespread adoption of encrypted web browsing via [[TLS/SSL|TLS/SSL]] certificates, making online shopping and banking feel secure for millions. The protocol's influence extends to secure email protocols like [[STARTTLS|STARTTLS]] and VPNs, forming the bedrock of trust in the digital age. Its elegance and mathematical rigor have inspired countless other cryptographic innovations, solidifying its status as an iconic technological achievement. The very notion of a 'secure handshake' in digital interactions owes its existence to this 1976 breakthrough.
⚡ Current State & Latest Developments
In 2024, Diffie-Hellman, particularly its ephemeral variant (DHE), is being deprecated in favor of stronger security methods. The ongoing transition to [[TLS 1.3|TLS 1.3]] has standardized the use of ephemeral Diffie-Hellman, phasing out static DH key exchanges that were susceptible to passive eavesdropping and later decryption. However, the cryptographic community is increasingly focused on post-quantum cryptography, which aims to develop algorithms resistant to attacks from future quantum computers. While DH itself is not directly vulnerable to current quantum algorithms like Shor's algorithm (which targets [[RSA (cryptography)|RSA]] and [[Elliptic-curve cryptography|ECC]] discrete logarithms), the underlying mathematical problems are related. Consequently, research into quantum-resistant key exchange mechanisms, such as those based on [[Lattice-based cryptography|lattices]] or [[code-based cryptography|coding theory]], is accelerating.
🤔 Controversies & Debates
A significant controversy surrounding Diffie-Hellman revolves around its susceptibility to 'man-in-the-middle' (MITM) attacks if not properly authenticated. Because the protocol itself only establishes a shared secret, an attacker can impersonate both parties, intercepting and relaying messages without either legitimate party realizing. This is why DH is almost always used in conjunction with authentication mechanisms, such as digital certificates in [[TLS/SSL|TLS/SSL]] or pre-shared keys. Another debate concerns the long-term security of the discrete logarithm problem against future computational advancements, including potential breakthroughs in quantum computing, which has spurred the development of post-quantum cryptography. Furthermore, the choice of DH groups can be contentious; some older, smaller groups have been deprecated due to known vulnerabilities, leading to ongoing discussions about best practices and recommended group sizes.
🔮 Future Outlook & Predictions
The future of Diffie-Hellman is intertwined with the advent of quantum computing. While current quantum algorithms do not break standard DH, they pose a significant threat to related public-key systems like [[RSA (cryptography)|RSA]] and [[Elliptic-curve cryptography|ECC]]. The cryptographic world is actively migrating towards post-quantum cryptography (PQC) standards, which include quantum-resistant key exchange algorithms. NIST's PQC standardization process, for example, is selecting algorithms that are believed to be secure against both classical and quantum computers. It's likely that DH, in its current form, will gradually be supplemented or replaced by PQC alternatives for long-term security guarantees. However, DH's foundational principles will undoubtedly continue to influence the design of future secure communication protocols, potentially in hybrid approaches combining classical and PQC methods.
💡 Practical Applications
Diffie-Hellman key exchange is the invisible engine behind much of our secure digital infrastructure. Its most ubiquitous application is in establishing secure sessions for [[Transport Layer Security|TLS]], the protocol that secures web traffic (HTTPS) for websites like [[google-com|Google.com]] and [[amazon-com|Amazon.com]]. It's also fundamental to securing Virtual Private Networks (VPNs), enabling remote workers to connect securely to corporate networks. Secure Shell (SSH) connections for remote server administration rely on DH for key establishment. Furthermore, it's used in secure messaging applications and for establishing secure channels in various communication protocols, ensuring that sensitive data transmitted over public networks remains confidential and uncompromised by eavesdroppers.
Key Facts
- Category
- technology
- Type
- topic